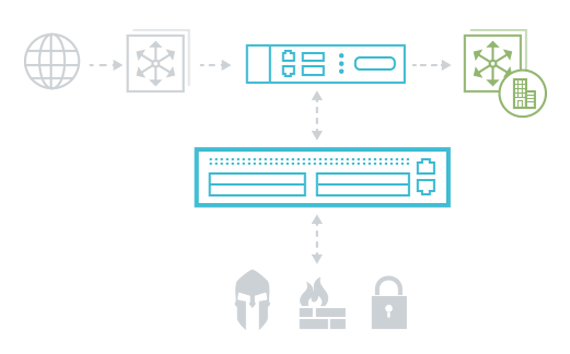
INLINE SECURITY DEPLOYMENT SCENARIOS
Learn more about the benefits of inline security in the following scenarios.

REDUCE SECURITY ALERTS
Pre-filtering traffic keeps security tools from being overwhelmed and helps staff focus on high-priority alerts. Find out more.

ENSURE CONTINUOUS INSPECTION
When every second counts, make sure you maintain security inspection during hardware or software failures. Find out more.

MAXIMIZE TOOL EFFICIENCY
Intelligent traffic filtering reduces the workload on your security tools and maximizes their efficiency. Find out more.
THE IMPORTANCE OF RESILIENCE
Will you still be protected if your security infrastructure suffers a temporary outage? Or be able to upgrade without service disruption? Make sure security and monitoring tools can recover from unexpected disruptions with the industry's fastest failover.

UPGRADE WITHOUT DOWNTIME
Did you know you can upgrade and maintain your security solutions without disrupting network availability or waiting for a maintenance window? Deploying an external bypass in front of inline security tools lets you route traffic around any device you need to take offline.
THE VALUE OF INLINE SECURITY
Financial Services Firm Reduces CAPEX on Tools by $680K
Deploying a security architecture let this company chain inline security tools together to increase efficiency.
Healthcare Provider Eliminates $1.5M in Compliance Fines
High availability deployment of next gen firewall satisfies need for robust threat detection.
Infographic: Upgrading Your Firewall is Half the Battle
Upgrading your firewalls or migrating to NGFWs can be the perfect time to deploy a more robust inline security architecture.
RELATED INFORMATION
WEBINARS
Dark Reading + Ixia: Resilient Security Monitoring: One Step at a Time
Upgrading Your Firewall? It's Time for an Inline Security Fabric
WHITE PAPERS
Deploying Inline Security Architecture: Key Considerations
Security Resilience—The Paradigm Shift is Here
Best Practices for Security Resilience
Unmasking Network and Data Evasions
Simulating a DDoS Attack in Your Own Lab
Improving Network Security Threat Detection
TECH PARTNER COLLATERAL
Best Practice Deployment Guide: Imperva + Ixia
ProtectWise and Ixia - Disrupting Network Security
Palo Alto Networks Solution Brief
RSA NetWitness and Ixia Solution Brief
INFOGRAPHICS
Anatomy of Ixia’s Application Intelligence
Botnet: Is Your Company’s Network Next?
Upgrading Your Firewall is Half the Battle
SOLUTION BRIEFS
Creating Resilience Within A Security Architecture
Get More Value from Security and Monitoring Tools
High Availability Makes Monitoring More Reliable
Strengthen Security and Reduce Risk of Downtime
CASE STUDIES
Customer Secures Their Network From Cradle to Grave
Service Provider Strengthens Defense Against Cyber attacks
Strengthen Security Tools In 30 Minutes
Manufacturer Chooses Bypass for Next Gen Firewall Deployment
EBOOKS / REPRINTS
BLOG POSTS
2.5 million reasons why it’s critical to boost DDoS defenses
Blocking the Rise of Ransomware
External bypass switch: Unsung hero of security monitoring
We can help you build a security architecture that delivers relevant data at high speed, with complete resiliency.